In this article, we’ll guide you on how to integrate AssetSonar with Azure Active Directory (AD). When you integrate AssetSonar with Azure AD, you can:
- Control in Azure AD who has access to AssetSonar.
- Enable your users to be automatically signed-in to AssetSonar with their Azure AD accounts.
- Manage your accounts in one central location i.e. the Azure portal.
To learn more about Single Sign-on with Azure AD, click here.
1. Prerequisites
To get started, you need the following items:
- An Azure AD subscription. If you don’t have a subscription, you can get a free account.
- AssetSonar single sign-on (SSO) enabled subscription.
2. Scenario description
In this article, you configure and test Azure AD SSO in a test environment.
- AssetSonar supports Service Provider initiated SSO
- AssetSonar supports Just In Time user provisioning
Note: The identifier of this application is a fixed string value so only one instance can be configured in one tenant.
3. Adding AssetSonar from the gallery
To configure the integration of AssetSonar into Azure AD, you need to add AssetSonar from the Azure Gallery to your list of managed SaaS apps.
- Sign in to the Azure portal using either a work or school account, or a personal Microsoft account.

2. On the left navigation pane, select the ‘Azure Active Directory’ service.
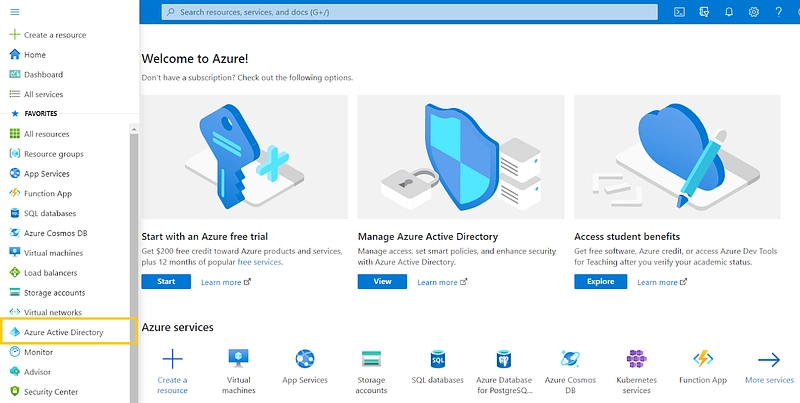
3. Navigate to ‘Enterprise Applications’.

4. Then, select ‘All Applications’.

5. To add a new application, select ‘New application’.

6. In the Browse Azure AD Gallery section, type ‘AssetSonar’ in the search box.

7. Select AssetSonar from the results panel and then add the app by hitting ‘Create’.
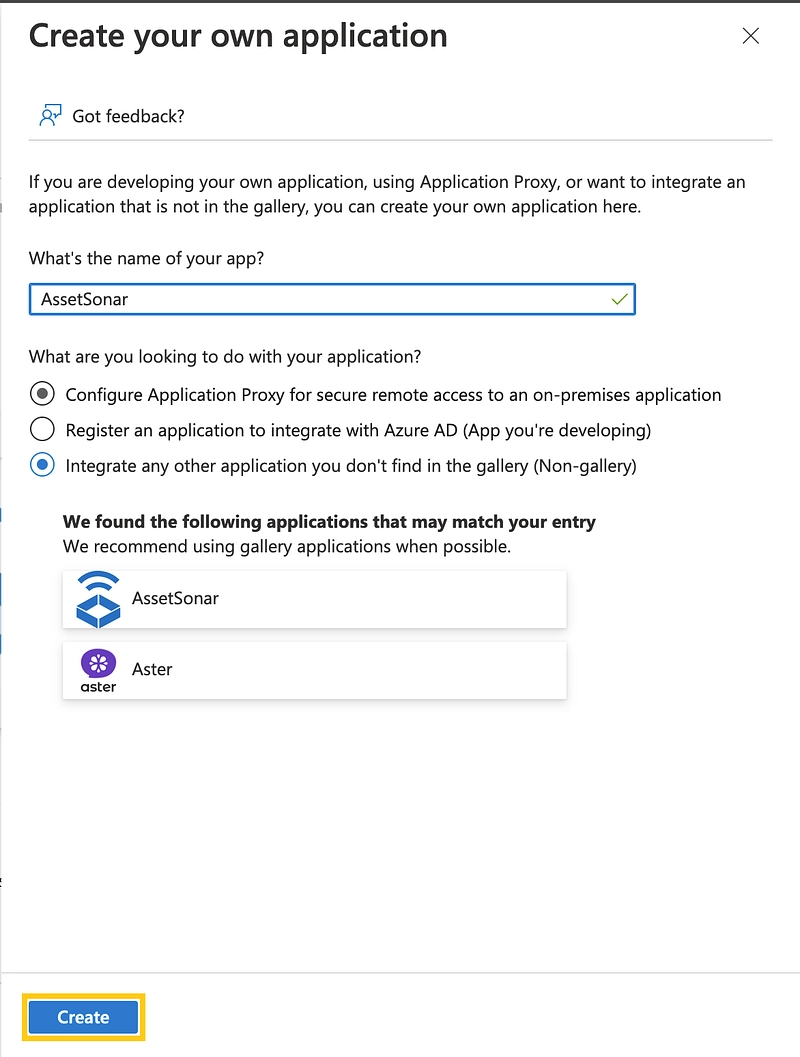
Wait a few seconds while the app is added to your tenant.
Note: If you want to use SCIM along with SAML, you would have to create a new custom application for SCIM.
4. Configure and test Azure AD single sign-on for AssetSonar
Configure and test Azure AD SSO with AssetSonar using a test user, let’s call him, Ray Holt. For SSO to work, you need to establish a link relationship between an Azure AD user and the related user in AssetSonar.
To configure and test Azure AD SSO with AssetSonar, complete the following building blocks:
- Configure Azure AD SSO to enable your users to use this feature.
– Create an Azure AD test user — to test Azure AD single sign-on with Ray Holt.
– Assign the Azure AD test user — to enable Ray Holt to use Azure AD single sign-on. - Configure AssetSonar SSO to configure the single sign-on settings on the AssetSonar application side.
– Create an AssetSonar test user to have a counterpart of Ray Holt in AssetSonar that is linked to the Azure AD representation of a user. - Test SSO to verify whether the configuration works.
5. Configure Azure AD SSO
Follow these steps to enable Azure AD SSO in the Azure portal.
- In the Azure portal, on the AssetSonar application integration page, find the Manage section and select ‘Single sign-on’.

2. On the Select a single sign-on method page, select ‘SAML’.

3. On the Set up single sign-on with SAML page, click the ‘Edit’ icon for Basic SAML Configuration to edit the settings.

4. On the Basic SAML Configuration section, enter the values for the following fields:
4.1. For Service Provider Initiated configuration:

Type the following in these data fields:
- Identifier (Entity ID): https://www.assetsonar.com
- Reply URL (Assertion Consumer Service URL): https://<SUBDOMAIN>.assetsonar.com/users/auth/saml/callback
- Sign-on URL: https://<SUBDOMAIN>.assetsonar.com/users/sign_in
Note: Replace the “subdomain” text with the subdomain in your company’s AssetSonar account URL. You can also contact the AssetSonar team at support@ezo.io for this value. Refer to the patterns displayed in the Basic SAML Configuration section in the Azure portal for additional fields.
4.2. For IDP Initiated configuration:

In order to sign in directly upon initiating from the IdP (Azure AD). We need to change the sign-on URL in Azure AD to “https://<SUBDOMAIN>.assetsonar.com/users/auth/saml”.
5. AssetSonar application expects the SAML assertions in a specific format, which requires you to add custom attribute mappings to your SAML token attributes configuration. The following screenshot shows the list of default attributes. Click ‘Edit’.

Copy the claim name URLs for user.givenname, user.surname, and user.mail and paste them onto the Attributes fields required in Step 5 of Section 6.3.
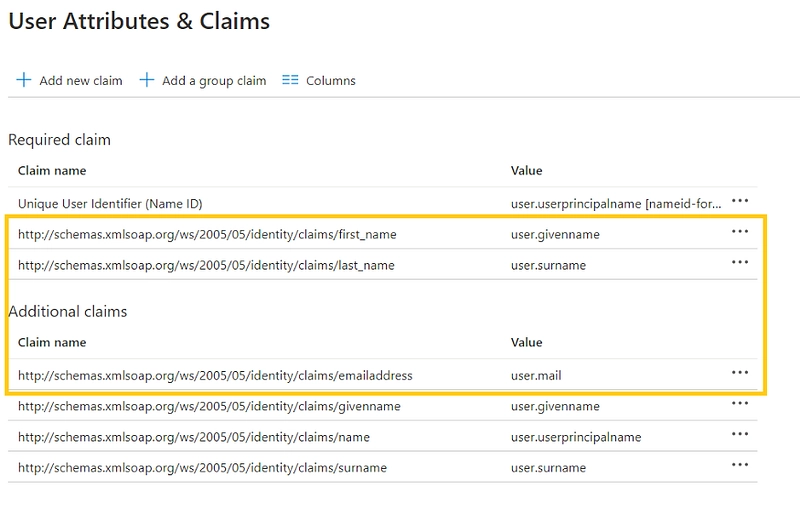
6. In addition to the above, the AssetSonar application expects a few more attributes to be passed back in the SAML response (shown below). These attributes are also pre-populated but you can review them as per your requirements.
7. On the Set up single sign-on with SAML page, in the SAML Signing Certificate section, click on ‘Add Certificate’, find Certificate (Base64), select ‘Download’ to download the certificate, and save it on your computer for Step 2 of Section 6.3.

8. On the ‘Set up AssetSonar’ section, copy the Login URL for Step 1 of Section 6.3.

5.1. Create an Azure AD test user
In this section, you’ll create a test user called Ray Holt in the Azure portal.
- From the left pane in the Azure portal, select Azure Active Directory, select Users, and then select All users.

2. Select ‘New user’ at the top of the screen.

3. In the User properties, follow these steps:
- In the Name field, enter ‘Ray Holt’.
- In the User name field, enter the username@companydomain.extension. For example, ‘rayholt@assetsonar.com’.

- Select the Show password check box, and then write down the value that’s displayed in the Password box.

- Click ‘Create’.

5.2. Assign the Azure AD test user
In this section, you’ll enable Ray Holt to use Azure single sign-on by granting access to AssetSonar.
- In the Azure portal, select Enterprise Applications, and then select All applications.
- In the applications list, select AssetSonar.
- In the app’s overview page, find the Manage section, and select ‘Users and groups’.

4. Select ‘Add User’, then select Users and groups in the Add Assignment dialog.

5. In the Users and groups dialog, select Ray Holt from the Users list, then click the ‘Select’ button at the bottom of the screen.
6. If you’re expecting any role value in the SAML assertion, in the Select Role dialog, select the appropriate role for the user from the list and then click the Select button at the bottom of the screen.
7. In the Add Assignment dialog, click the ‘Assign’ button.

6. Configure AssetSonar SSO
Once you have set up the AssetSonar app on your preferred SAML identity provider i.e. Azure AD in this instance, configure the settings in AssetSonar from Settings → Add Ons → SAML Integration.

6.1. Whitelisting the IPs on SAML
Some identity providers require IPs to be whitelisted. Make sure that the following two IPs are whitelisted in your SAML settings:
1. 18.204.232.104
2. 52.45.242.87
6.2. Add AssetSonar consumer service URL to your SAML Settings in Azure AD
The AssetSonar consumer service URL can be obtained from Settings → Add Ons → SAML Integration:
https://<Your Company Subdomain>.assetsonar.com/users/auth/saml/callback
Copy and paste the AssetSonar consumer service URL in the Reply URL field from Step 4 of Section 5.1.
6.3. Fill in the configuration settings
The following information needs to be configured in your AssetSonar’s account (see image below to identify the fields):

1. Unique Identity Provider URL: Find and copy your Login URL from Step 8 of Section 5.1 (see the image below). You will be required to paste this link in the ‘Identity Provider URL’ field while configuring AssetSonar for SAML Integration.

2. Identity Provider Certificate: Unique for every Account Owner, this certificate is provided by the identity provider. Copy the text from Certificate (Base64) that you downloaded and saved from Step 7 of Section 5.1. (see image below).

AssetSonar will use the certificate to validate the response from your identity provider letting the user to login in using SAML.
Note: Make sure to follow the below format for the certificate when pasting it in the certificate field so AssetSonar validates your identity provider’s certificate without any error. It’s as follows:
— –BEGIN CERTIFICATE — –
your certificate details here
— –END CERTIFICATE — –
3. Login Button Text: By default, it’s labeled as ‘Access through SAML SSO’. You can rename it to any text preferable to you e.g. Access using Ray Holt Corp Login.
4. Clock Drift: A delay of a few seconds in situations when different time zones are involved to ensure that the response generated by a server remains valid.
5. Attributes required for SAML configuration: Last Name and Email attributes need to be present for AssetSonar. These attributes/parameters should be sent over to AssetSonar from your identity provider. In Azure AD, you can copy these parameters from Step 5 and 6 of Section 5.1. Map these parameters in AssetSonar. If your Last Name attribute in SAML is last_name, then fill in ‘last_name’ against the Last Name field. The same goes for the Email.
6. AssetSonar Role by default: This option lets you add users as either Administrators or Staff Users.
Scroll to the top of the Add Ons page in AssetSonar settings, and click ‘Update’. You now have a SAML-enabled AssetSonar account.
This is how your SAML configuration settings should look like:

6.4. Create AssetSonar test user
In this section, a user called Ray Holt is created in AssetSonar. AssetSonar supports just-in-time user provisioning, which is enabled by default. There is no action item for you in this section. If a user doesn’t already exist in AssetSonar, a new one is created after authentication.
7. Test SSO
In this section, you test your Azure AD single sign-on configuration using the Access Panel.
When you click the AssetSonar tile in the Access Panel, you should be automatically signed in to the AssetSonar for which you set up SSO. For more information about the Access Panel, see Introduction to the Access Panel.
8. Troubleshooting
This section highlights a common issue that you may come across while configuring the SAML integration with Azure AD, and ways to fix it.
Problem: I managed to configure the SAML integration with Azure AD, but I can’t seem to log into the AssetSonar portal.
Solution: If you have configured SAML 2.0 in Azure AD but failed to log into AssetSonar, it may be because your Attributes have not been configured correctly. These Attributes are used to verify the existence of user accounts on both platforms — Azure AD and AssetSonar — and should be identical in both applications.
In case of a discrepancy, you won’t be able to log in and will receive an email from our support team. This email lists the values we receive from the SAML payload of your server in the form of a table and highlights the Attribute(s) that have been incorrectly figured. You need the correct Attribute for each corresponding Value (such as Email, Last Name, and First Name).
For instance, in the image below, we have highlighted the incorrectly configured Attribute corresponding to the ‘Email’ value.

The email also shows the incorrectly configured attribute value as it appears in AssetSonar and flags it with “ATTRIBUTE NOT FOUND” so you can re-enter the correct value in AssetSonar SAML settings.

As you can see, the configured Attribute for Email is different in both images, resulting in the login failure.
To fix this, copy and paste the Claim Name URL for Email (see image below) from your Azure AD account into AssetSonar’s section for SAML integration and hit ‘Update’. You can now successfully log into AssetSonar using your Azure AD email.
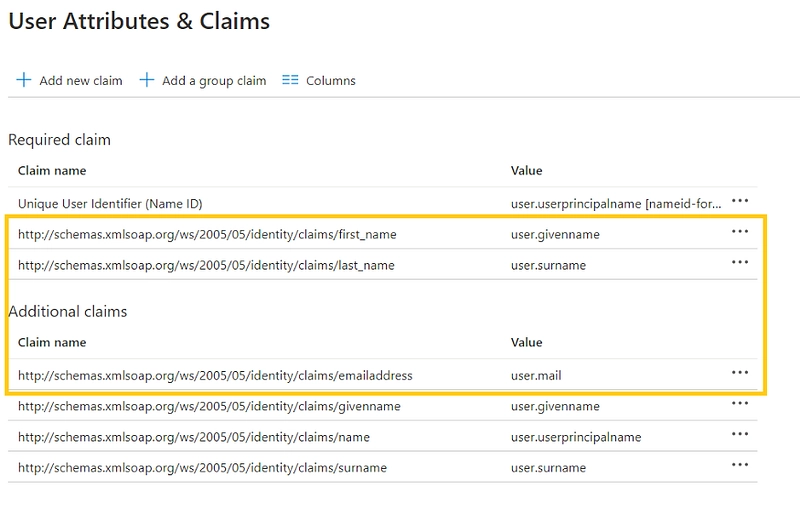
Please note that for the integration to work correctly, you MUST enter all Attribute values in AssetSonar exactly as they appear in Azure AD.
Read more: [How-to] Implement User Provisioning via SCIM with OneLogin in AssetSonar
About AssetSonar
AssetSonar is the leading IT asset management solution used by IT-intensive organizations and businesses all over the globe.
For more assistance, drop us an email at support@ezo.io.


