Network administrators use Active Directories to streamline maintenance processes within large organizations. Instead of having to perform several updates manually, a network admin can update one object in a single process.
Active Directories are used to allow or deny application access to end-users through the network trees. They help in keeping a large network organized and maintained. And you can do this without having to perform each task through an individual process.
1. Why do you need AD DS?
Active Directory Domain Services (AD DS) is a server role in Active Directory. It allows admins to manage and store information about resources. These resources come from a network, as well as application data – in a distributed database.
AD DS can also help Admins manage a network’s elements (computers and end-users). They can reorder them into a custom hierarchy.
Technical professionals from different industries run apps using different platforms. As of 2019, 52 percent of them are currently running apps using Microsoft Azure – a cloud platform service. Azure AD DS is part of this platform!
2. What is Azure AD?
Azure AD is a highly-secure identity and access management cloud solution. It combines core directory services, advanced identity governance, and application access management.
Its design purpose from the ground up is to be secure, scalable, and cross-platform. Azure AD is a cloud-based directory and identity management service from Microsoft. It combines core directory services, access management, and identity protection – all into a single solution.
It gives your people, partners, and customers a single identity for accessing the apps. Apps they want and can collaborate from any platform and device.
It is based on scalable management capabilities and risk-based access rules. This enables Azure AD to ensure security and streamline IT processes.
3. What can you do with Azure AD?
- Centralize identity management
- Enable Single Sign-On
- Turn on conditional access
- Manage access at scale
- Enable password management
- Use role-based access control
- Use pre-integrated SaaS apps
- Lower exposure of privileged accounts
- Keep track of suspicious activities
4. Benefits of using Azure AD
- A cloud-connected, seamless authentication experience
- Remote access to your on-premise apps
- Cross-organizational collaboration
- Self-service capabilities
- Secure user lifecycle management
- Scalable identity and access management
- Cloud-powered identity protection
Learn more about Cloud Identity and Access Management [Infographic]
5. Pre-requisites
To configure secure LDAP, you need the following resources and privileges:
- An active Azure subscription. If you don’t have an Azure subscription, create an account.
- An Azure Active Directory tenant associated with your subscription. It should be either synchronized with an on-premises directory or a cloud-only directory. Create an Azure Active Directory tenant or associate an Azure subscription with your account.
- An Azure Active Directory Domain Services managed domain enabled and configured in your Azure AD tenant. If needed, create and configure an Azure Active Directory Domain Services instance.
- The LDP.exe tool installed on your computer. Install the Remote Server Administration Tools (RSAT) for AD Domain Services and LDAP.
To better understand Azure AD and its documentation, we recommend reviewing the terms mentioned here.
6. Configuring LDAP on Azure AD
6.1. Creating a certificate for secure LDAP
Creating a certificate requires to run a set of commands on Windows Powershell.
1. Open a PowerShell window as Administrator and run the following commands one by one.

2. Replace the $dnsName variable with the DNS name used by your own managed domain, such as onmicrosoft.com.

6.2. Exporting a certificate for Azure AD DS
Now you need to export the certificate to a (.PFX) certificate file that includes the private key. You must do this before you can use the digital certificate created with your Azure AD DS managed domain.
1. To open the Run dialog, select the Windows and R keys.
2. Open the Microsoft Management Console (MMC) by entering mmc in the Run dialog, then select OK.
3. On the User Account Control prompt, click Yes to launch MMC as administrator.
4. From the File menu, click Add/Remove Snap-in.
5. In the Certificates snap-in wizard, choose Computer account, then select Next.
6. On the Select Computer page, choose Local computer: (the computer this console is running on). Then select Finish.
7. In the Add or Remove snap-in dialog, click OK to add the certificates snap-in to MMC.

8. In the MMC window, expand Console Root. Select Certificates (Local Computer). Then expand the Personal node, followed by the Certificates node.

9. You will see the self-signed certificate created in the previous step, such as onmicrosoft.com. Right-select this certificate, then choose All Tasks > Export.
10. In the Certificate Export Wizard, select Next.
11. You must export the private key for the certificate. Without the private key in the exported certificate, the action to enable secure LDAP for your managed domain will fail.
On the Export Private Key page, choose Yes > export the private key, then select Next.
12. Azure AD DS managed domains only support the (.PFX) certificate file format that includes the private key. Don’t export the certificate as .CER certificate file format without the private key.

On the Export File Format page, select Personal Information Exchange – PKCS #12 (.PFX) as the file format for the exported certificate. Check the box for Include all certificates in the certification path if possible.
13. You are using this certificate to decrypt data. You should be careful when controlling access. You can use a password to protect the use of the certificate. Without the correct password, you cannot apply the certificate to a service.
14. On the Security page, choose the option for Password to protect the (.PFX) certificate file. Enter and confirm a password, then select Next. We’ll use this password in the next section to enable secure LDAP for your Azure AD DS managed domain.
15. On the File to Export page, specify the file name and location. It’s where you’d like to export the certificate, such as C:\Users\accountname\azure-ad-ds.pfx.
16. On the review page, select Finish to export the certificate to a (.PFX) certificate file. You will see a confirmation dialog when the certificate has been successfully exported.
6.3. Exporting a certificate for client computers
Now we will follow the same steps for the client certificate with a little bit of alternation.
1. Go back to the MMC for Certificates (Local Computer) > Personal > Certificates store. You will see the self-signed certificate created in a previous step, such as onmicrosoft.com. Right-select this certificate, then choose All Tasks > Export.
2. In the Certificate Export Wizard, select Next.
3. You do not need the private key for clients. On the Export Private Key page, choose No, do not export the private key, then select Next.

4. On the Export File Format page, select Base-64 encoded X.509 (.CER) as the file format – for the exported certificate.
5. On the File to Export page, specify the file name and location. For example, C:\Users\accountname\azure-ad-ds-client.cer.
6. On the review page, select Finish to export the certificate to a (.CER) certificate file. You will see a confirmation dialog when the certificate exported is successful.
You can now distribute the (.CER) certificate file to client computers. Computers that need to trust the secure LDAP connection to the Azure AD DS managed domains.
Let’s install the certificate on the local computer.
- Open File Explorer and browse to the location where you saved the (.CER) certificate file. Such as C:\Users\accountname\azure-ad-ds-client.cer.
- Right-select the (.CER) certificate file, then choose Install Certificate.
- In the Certificate Import Wizard, choose the certificate in the Local machine. Then select Next.
- When prompted, choose Yes to allow the computer to make changes.
- Choose to Automatically select the certificate store based on the type of certificate. Then, select Next.
- On the review page, select Finish to import the (.CER) certificate file. You will see a confirmation dialog when the certificate has been successfully imported.
6.4. Enabling secure LDAP for Azure AD DS
Now that you have created and exported a digital certificate – and a client computer, let’s move to the next step. You now have to enable secure LDAP on your Azure AD DS managed domain.

1. In the Azure portal, search for domain services in the Search resources box. Select Azure AD Domain Services from the search result.
2. Choose your managed domain, such as onmicrosoft.com.
3. On the left-hand side of the Azure AD DS window, choose Secure LDAP.
4. By default, secure LDAP access to your managed domain is disabled. Toggle Secure LDAP to Enable.
Toggle Allow secure LDAP access over the internet to Enable.
5. In the next step, you’ll have to configure a network security group. This is to lock down access to only the required source IP address ranges.
Toggle Allow secure LDAP access over the internet to Enable.
6. Select the folder icon next to (.PFX) file with secure LDAP certificate. You have to browse to the path of the (.PFX) file. Then, select the certificate created in a previous step that includes the private key.
7. Enter the Password to decrypt (.PFX) file set in a previous step when you exported the certificate to a (.PFX) file.

8. Select Save at the top to enable secure LDAP.
You will see a notification that secure LDAP is being configured for the managed domain. You cannot change other settings for the managed domain until the process completes.
Note: It takes a few minutes to enable secure LDAP for your managed domain.
6.5. Whitelisting IPs on Azure for secure LDAP access over the internet
The managed domain is reachable from the internet on TCP port 636. It’s recommended to restrict access to the managed domain.
Let’s create a rule to allow inbound secure LDAP access over TCP port 636 from a specified set of IP addresses.
1. In the Azure portal, select Resource groups on the left-hand side navigation.
2. Choose your resource group, such as myResourceGroup. Then select your network security group, such as AADDS-onmicrosoft.com-NSG.
3. You will see the list of existing inbound and outbound security rules. On the left-hand side of the network security group windows, choose Security > Inbound security rules.
4. Select Add, then create a rule to allow TCP port 636.
For improved security, choose the source as IP Addresses. And then specify your own valid IP address or range for your organization.

Tip: Type myip on Google.com if you don’t know your public IP Address.

5. Select Add at the bottom-right to save and apply the rule.
6.6. Configuring DNS zone for external access
With secure LDAP access enabled over the internet, you now have to update the DNS zone. This will enable the client computers to find this managed domain.
Secure LDAP (LDAPS) is a connection protocol. It is used between the application and Network Directory/Domain Controller – within the infrastructure.
You will see the Secure LDAP external IP address listed on the Properties tab.

1. Go to the properties of your domain and copy the mentioned Secure LDAP external IP. For example:
2. Add the IP in your host file located at “C:\Windows\System32\drivers\etc”.
6.7. Testing queries to the managed domain
To connect your Azure AD DS managed domain and search over LDAP, you need to use the LDP.exe too.
If you don’t have LDP.exe installed, install it from here.
1. Open LDP.exe and connect to the managed domain. Select Connection, then choose Connect.
2. Enter the secure LDAP DNS domain name of your managed domain – created in the previous step. Such as ldaps.onmicrosoft.com.
To use secure LDAP, set Port to 636, then check the box for SSL.

3. Select OK to connect to the managed domain. The following output will occur.
6.8. Binding users to the managed domain
To bind a user with ldp.exe, you need to have at least one user exist in the Active Directory.
1. To create a user, go to Azure Active Directory in your account.
2. Select Users under Manage on the left panel. Then click +New User > Create User to create a user of type Member.

Please note that the user type should not be a guest user.

3. Reset the user password once you have created a new user. To do that, select the user and then click Reset Password on the profile page.
4. With the new user created in the AD, the user will now have to log in to the account using PowerShell.
5. Run Windows PowerShell, as an administrator.
6. Enter the following command to log in to your Azure account.
→ Login-AzAccount

7. Then, enter your credentials. Once logged in, you will receive the following output:

8. Please make sure you have enabled your NTLM password hash synchronization. To enable it, enter the following commands:
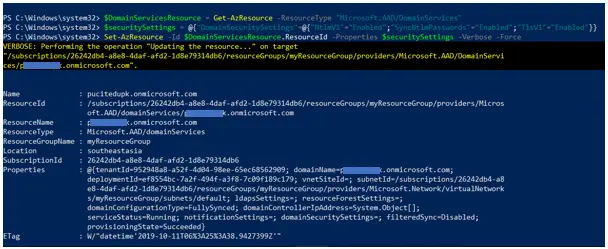
You should see the following output:
We recommend that you wait for a couple of minutes and then run ldp.exe.
9. Enter the username, only the part before @.
10. Enter the password and the domain name.

11. Choose the Bind type as Binding with credentials and click Enter. On successful binding, you should see the following output on screen:
Once you are able to bind the connection, you can find your DN from the View tab > Tree. Follow the steps below:
- Let the base Dn be empty.
- Expand the explorer view on the left-side and select OU=AADDC Users.
- Here, you will find the list of all DN(s) of your users. Below is what you should see:
- Copy the required DN and paste it into the EZO settings – for LDAP Admin Login (Complete DN).

- Use password of the same Microsoft account for which you acquired the DN details.
Read more: Troubleshooting Issues related to Azure AD
7. Integrating LDAP server with EZO
The step forward is to integrate your Azure AD with EZO. This integration will enable you to ‘sync’ your staff database with EZO. It will help you avoid replicating LDAP staff members in EZO.
Enable LDAP Server Integration from Settings → Add Ons.
Learn more about integrating LDAP Server with EZO
Have any questions?
For more assistance, drop us an email at support@ezo.io.
Was this helpful?
- 1. Why do you need AD DS?
- 2. What is Azure AD?
- 3. What can you do with Azure AD?
- 4. Benefits of using Azure AD
- 5. Pre-requisites
- 6. Configuring LDAP on Azure AD
- 6.1. Creating a certificate for secure LDAP
- 6.2. Exporting a certificate for Azure AD DS
- 6.3. Exporting a certificate for client computers
- 6.4. Enabling secure LDAP for Azure AD DS
- 6.5. Whitelisting IPs on Azure for secure LDAP access over the internet
- 6.6. Configuring DNS zone for external access
- 6.7. Testing queries to the managed domain
- 6.8. Binding users to the managed domain
- 7. Integrating LDAP server with EZO